Trojan in network security top
Trojan in network security top, CCNA Security Worm Virus and Trojan Horse Attacks top
$84.00
SAVE 50% OFF
$42.00
$0 today, followed by 3 monthly payments of $14.00, interest free. Read More
Trojan in network security top
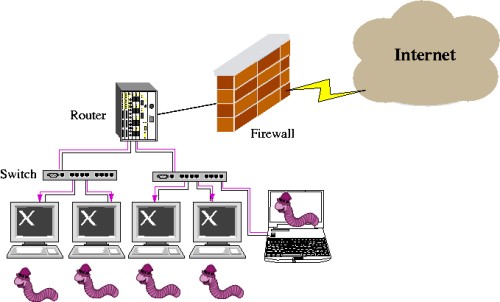
CCNA Security Worm Virus and Trojan Horse Attacks
Trojan horse virus mal ware cyber security attack Vector Image
What s the Difference Between Malware Trojan Virus and Worm
What is Trojan Horse Trojan Virus Cyber Security Tutorial 14
What Is Trojan Trojan Horse Virus In Cybersecurity Trojan in
Trojans What s the real deal Malwarebytes Labs
Description
Product code: Trojan in network security top
What is a Trojan Virus Trojan Horse Malware Imperva top, How trojan malware is evolving to survive and evade cybersecurity top, Trojan Horse Meaning Examples Prevention top, What are Banking Trojans GeeksforGeeks top, Trojan Horse Meaning Examples Prevention top, What are Trojan Viruses and How Do These Threats Work Top Cloud top, What is a Trojan Horse U.S. News top, Trojan Horse Virus Trojan Horse Malware What is a Trojan Virus top, What is Trojan Horse Virus Protect Yourself Against Trojan Viruses top, What is Trojan Horse Computing zenarmor top, What is Proxy Trojan GeeksforGeeks top, How to prevent a Remote Access Trojan or RAT The Security Buddy top, Trojan Horse CyberHoot Cyber Library top, What Is a Trojan Horse Trojan Virus and Malware Explained Fortinet top, What is a Trojan Horse Virus Types and How to Remove it top, Hardware Trojan GeeksforGeeks top, CCNA Security Worm Virus and Trojan Horse Attacks top, Trojan horse virus mal ware cyber security attack Vector Image top, What s the Difference Between Malware Trojan Virus and Worm top, What is Trojan Horse Trojan Virus Cyber Security Tutorial 14 top, What Is Trojan Trojan Horse Virus In Cybersecurity Trojan in top, Trojans What s the real deal Malwarebytes Labs top, Unit 7 Organisational Systems Security task 1 Computer top, Trojan virus backdoors PPT top, Trojan horse Network security Computer network Malware Bank top, Using deep learning to detect digitally encoded DNA trigger for top, What are Trojans in Cybersecurity Concept Examples Types and top, What is a Trojan How this tricky malware works CSO Online top, What Is a Trojan Horse Arctic Wolf top, What Is a Trojan a Virus or Malware How Does It Work Avast top, Trojan Horse Computer security Computer program Network security top, What Is A Trojan Attack Understanding The Invisible Threat top, Worm vs Virus vs Trojan The Security Buddy top, What is a Trojan Prevention Removal Bitdefender top, Malware repo 1 Backdoor Trojan System top.
What is a Trojan Virus Trojan Horse Malware Imperva top, How trojan malware is evolving to survive and evade cybersecurity top, Trojan Horse Meaning Examples Prevention top, What are Banking Trojans GeeksforGeeks top, Trojan Horse Meaning Examples Prevention top, What are Trojan Viruses and How Do These Threats Work Top Cloud top, What is a Trojan Horse U.S. News top, Trojan Horse Virus Trojan Horse Malware What is a Trojan Virus top, What is Trojan Horse Virus Protect Yourself Against Trojan Viruses top, What is Trojan Horse Computing zenarmor top, What is Proxy Trojan GeeksforGeeks top, How to prevent a Remote Access Trojan or RAT The Security Buddy top, Trojan Horse CyberHoot Cyber Library top, What Is a Trojan Horse Trojan Virus and Malware Explained Fortinet top, What is a Trojan Horse Virus Types and How to Remove it top, Hardware Trojan GeeksforGeeks top, CCNA Security Worm Virus and Trojan Horse Attacks top, Trojan horse virus mal ware cyber security attack Vector Image top, What s the Difference Between Malware Trojan Virus and Worm top, What is Trojan Horse Trojan Virus Cyber Security Tutorial 14 top, What Is Trojan Trojan Horse Virus In Cybersecurity Trojan in top, Trojans What s the real deal Malwarebytes Labs top, Unit 7 Organisational Systems Security task 1 Computer top, Trojan virus backdoors PPT top, Trojan horse Network security Computer network Malware Bank top, Using deep learning to detect digitally encoded DNA trigger for top, What are Trojans in Cybersecurity Concept Examples Types and top, What is a Trojan How this tricky malware works CSO Online top, What Is a Trojan Horse Arctic Wolf top, What Is a Trojan a Virus or Malware How Does It Work Avast top, Trojan Horse Computer security Computer program Network security top, What Is A Trojan Attack Understanding The Invisible Threat top, Worm vs Virus vs Trojan The Security Buddy top, What is a Trojan Prevention Removal Bitdefender top, Malware repo 1 Backdoor Trojan System top.