Backdoor trojan horse top
Backdoor trojan horse top, Backdoors an overview ScienceDirect Topics top
$86.00
SAVE 50% OFF
$43.00
$0 today, followed by 3 monthly payments of $14.33, interest free. Read More
Backdoor trojan horse top
Backdoors an overview ScienceDirect Topics
What are Trojan Viruses and How Do These Threats Work Top Cloud
New Trojan Backdoor Malware Targets Mac OS X And Linux Steals
Trojans and backdoors PPT
Trojan Horse Virus Examples How to Defend Yourself
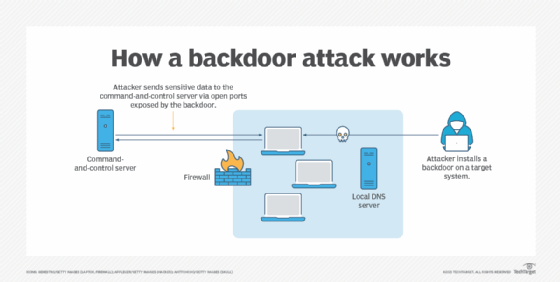
What is a Backdoor Attack Tips for Detection and Prevention
Description
Product code: Backdoor trojan horse top
What Is a Backdoor Attack Pro Tips for Detection Protection top, What is a Trojan horse virus Types of Cyber Threats ESET top, What Is a Backdoor Attack Pro Tips for Detection Protection top, What is a Trojan Virus Trojan Horse Malware Imperva top, What is a Backdoor Attack Shell Trojan Removal Imperva top, Trojans and backdoors PPT top, Tech Wreck InfoSec Blog Sample Trojan Horse Backdoor Types top, Trojan Horse Meaning Examples Prevention top, What is a Trojan Horse Virus Types and How to Remove it top, Trojan virus backdoors PPT top, Ravaging RDP Servers Backdoor Trojan Ramps Up Enterprise Risk top, What is a Trojan Horse Virus Types Prevention in 2024 top, What is Backdoor Attack Examples and Prevention top, Tech Wreck InfoSec Blog Sample Trojan Horse Backdoor Types top, Trojans Backdoors Rootkits Viruses and Worms ppt video online top, What Is a Backdoor Virus Backdoor Attack in 2024 top, Backdoors an overview ScienceDirect Topics top, What are Trojan Viruses and How Do These Threats Work Top Cloud top, New Trojan Backdoor Malware Targets Mac OS X And Linux Steals top, Trojans and backdoors PPT top, Trojan Horse Virus Examples How to Defend Yourself top, What is a Backdoor Attack Tips for Detection and Prevention top, Computer under attack trojan virus worm and backdoor Stock top, Trojan horse removal Protecting Troy top, Protect yourself against Trojan Horse attacks top, What Is a Trojan Horse Trojan Virus and Malware Explained Fortinet top, What Is a Backdoor Virus Definition Removal Example Video top, Preventing WordPress from Being Implanted with Backdoor Trojan top, How to Prevent Backdoor Attacks GeeksforGeeks top, Backdoor trojan linear icon. Malicious remote access to computer top, Backdoor trojan white linear icon for dark theme Vector Image top, Table 1 from A Comparison of Trojan Virus Behavior in Linux and top, Behind the Disguise of Trojans Radware Blog top, 2 364 Trojan Horse Isolated Images Stock Photos 3D objects top, What are Trojan Viruses and How Do These Threats Work Top Cloud top.
What Is a Backdoor Attack Pro Tips for Detection Protection top, What is a Trojan horse virus Types of Cyber Threats ESET top, What Is a Backdoor Attack Pro Tips for Detection Protection top, What is a Trojan Virus Trojan Horse Malware Imperva top, What is a Backdoor Attack Shell Trojan Removal Imperva top, Trojans and backdoors PPT top, Tech Wreck InfoSec Blog Sample Trojan Horse Backdoor Types top, Trojan Horse Meaning Examples Prevention top, What is a Trojan Horse Virus Types and How to Remove it top, Trojan virus backdoors PPT top, Ravaging RDP Servers Backdoor Trojan Ramps Up Enterprise Risk top, What is a Trojan Horse Virus Types Prevention in 2024 top, What is Backdoor Attack Examples and Prevention top, Tech Wreck InfoSec Blog Sample Trojan Horse Backdoor Types top, Trojans Backdoors Rootkits Viruses and Worms ppt video online top, What Is a Backdoor Virus Backdoor Attack in 2024 top, Backdoors an overview ScienceDirect Topics top, What are Trojan Viruses and How Do These Threats Work Top Cloud top, New Trojan Backdoor Malware Targets Mac OS X And Linux Steals top, Trojans and backdoors PPT top, Trojan Horse Virus Examples How to Defend Yourself top, What is a Backdoor Attack Tips for Detection and Prevention top, Computer under attack trojan virus worm and backdoor Stock top, Trojan horse removal Protecting Troy top, Protect yourself against Trojan Horse attacks top, What Is a Trojan Horse Trojan Virus and Malware Explained Fortinet top, What Is a Backdoor Virus Definition Removal Example Video top, Preventing WordPress from Being Implanted with Backdoor Trojan top, How to Prevent Backdoor Attacks GeeksforGeeks top, Backdoor trojan linear icon. Malicious remote access to computer top, Backdoor trojan white linear icon for dark theme Vector Image top, Table 1 from A Comparison of Trojan Virus Behavior in Linux and top, Behind the Disguise of Trojans Radware Blog top, 2 364 Trojan Horse Isolated Images Stock Photos 3D objects top, What are Trojan Viruses and How Do These Threats Work Top Cloud top.